CISO / Security Leader
Needs a clear, honest view of what is actually exposed, not just a dashboard score.
Wants proof: what got fixed, what is owned and what is consciously accepted.
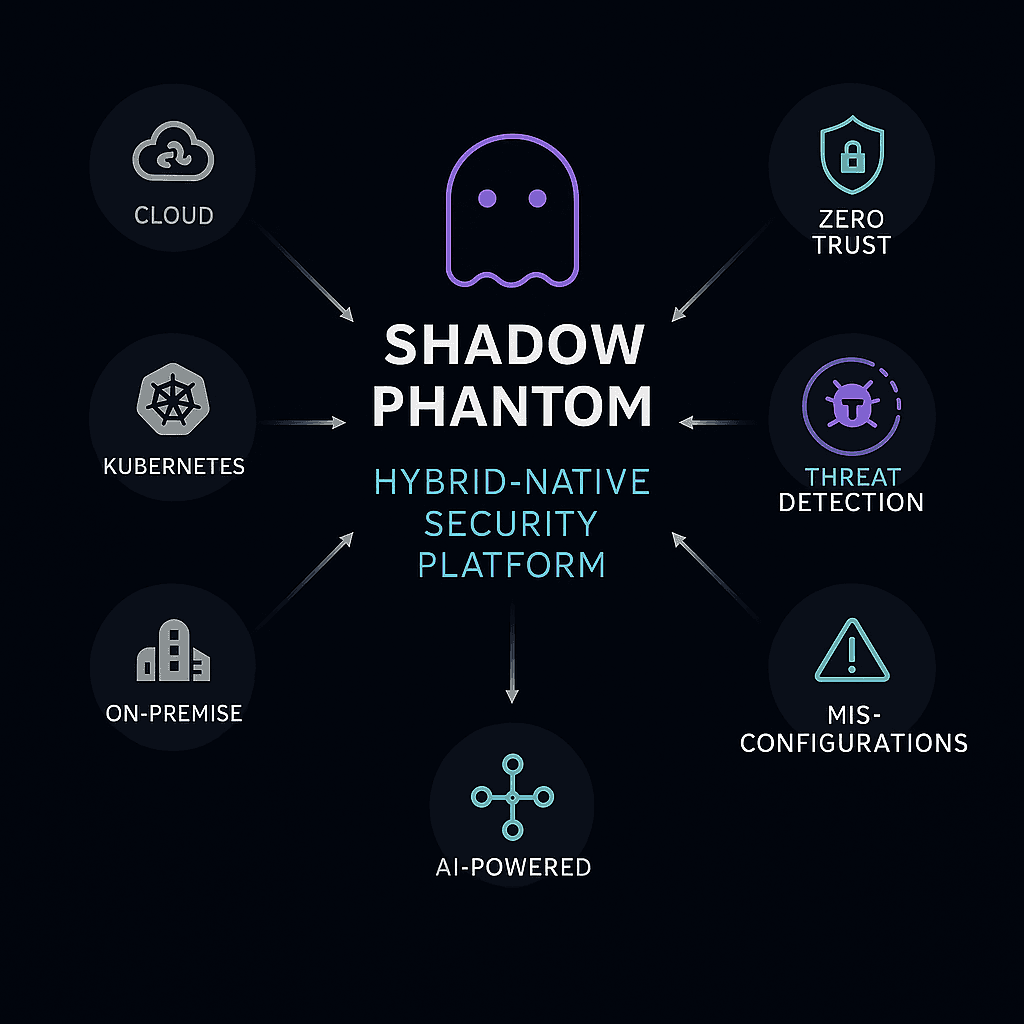
Shadow Phantom turns security blind spots into owned fixes across cloud and hybrid.
Detect what’s actually exposed, assign ownership, remediate safely and keep proof by default.
Shadow Phantom connects to the systems you already run and measures the real configuration state. Not what a policy document says. It highlights what’s genuinely risky and gives safe, practical paths to remediation (manual or automated), with proof.
Read-only, agentless connections into cloud, SaaS, Kubernetes, identity and on-prem. No endpoint agents. No rollout project.
Surface misconfigurations, policy gaps and drift with clear context on what’s exposed, why it matters and what to do next.
Every finding moves to: fixed, clearly owned or consciously accepted, with an audit trail by default.
Needs a clear, honest view of what is actually exposed, not just a dashboard score.
Wants proof: what got fixed, what is owned and what is consciously accepted.
Owns the reality of cloud, network and identity sprawl.
Needs guardrails and automation that don’t break SLAs or releases.
Has security work piling up in backlogs and pipelines.
Needs small, concrete changes teams can ship, with traceable outcomes.
Designs the “should be” but sees configs drift in the real world.
Needs a way to catch drift early without becoming “the blocker”.
Why Shadow Phantom exists
In modern environments, most issues don’t exist because teams lack tools. They exist because small things go unnoticed: misconfigurations, exposed assets, access drift and credentials that slip through the cracks.
Teams usually see these risks. The problem is what happens after: findings stack up, ownership is unclear and remediation slips down the backlog. Shadow Phantom is built to keep the loop closed, until each risk is fixed, clearly owned or consciously accepted.
Get started
Join the beta to see how Shadow Phantom turns exposure into owned outcomes. Fixed, owned or consciously accepted, with proof.
Connect cloud + identity (read-only). Start building a living inventory.
Get a ranked “top exposures” list with context, impact and ownership hints.
Ship concrete remediations with change windows, approvals and evidence.
Prevent drift: policy enforcement + recurring issue suppression + audit exports.
Outcome: fewer alerts • clearer ownership • faster fixes • audit-ready proof.
From signals to fixes, in one loop
Discover → Analyze → Organize → Respond → Enforce
A single security loop: find what exists, understand what matters, prioritize it, fix it safely and prevent it from coming back.
Map cloud + hybrid assets without agents. Keep it continuously updated.
You can’t secure what you don’t know exists.
Start with the highest-impact blind spots. Then expand coverage across cloud, identity, DevSecOps, infrastructure, SOC, compliance and AI assistance.
Find internet-exposed buckets, services and misconfigurations — then lock them down with a safe remediation path.
Explore this areaDetect shadow admin access and IAM drift with ownership and change-safe remediation.
Explore this areaDetect exposed secrets and reduce misconfig-driven risk with developer-facing fixes that teams can actually ship.
Explore this areaGet started
Let’s show you a short, actionable list your teams can execute on. With change-safe remediation and audit-ready evidence.
Every sector has its own mix of legacy systems, cloud initiatives and compliance pressure. Shadow Phantom adapts to that reality and helps teams reduce risk without slowing the business down.
Reduce exposure from IAM drift, leaked credentials and configuration gaps. Support audit readiness with evidence and clear ownership.
Learn MoreProtect sensitive data and workloads with continuous posture checks, safe remediation and traceable outcomes.
Learn MoreSecure hybrid OT-IT environments by detecting risky network paths, open ports and lateral movement opportunities.
Learn MoreEnforce security controls at scale across complex infrastructures with fast onboarding and audit-friendly reporting.
Learn MorePrevent shadow access to R&D and clinical systems with identity governance, drift detection and evidence trails.
Learn MoreReduce exposure from secrets, APIs and edge infrastructure while keeping teams shipping safely.
Learn MoreShift left with developer-facing fixes while keeping production posture controlled and traceable.
Learn MoreMost tools either give dashboards or more alerts. Shadow Phantom is built to do something simpler: show where your environment is actually weak and help teams fix it in a way operations and auditors can live with.
You get secure-by-design foundations, a tamper-evident trail and remediation workflows that respect how the business runs.
Actions and evidence are signed and stored append-only to support audit readiness and incident review.
RBAC, scoped access and tenant-aware controls across the platform.
Reduce alert fatigue by focusing on actionable, contextual issues, not raw telemetry.
Findings move to fixed, owned or consciously accepted, with traceability.
No endpoint agents. Outbound-only integrations via secure APIs.
Cloud, on-prem, OT and regulated environments, including constrained networks.
Approvals, change windows and rollback patterns to avoid breaking operations.
Integrate with tickets and pipelines for ownership and repeatability.
Clear, practical steps for engineers, not theoretical projects.
Automate fixes when validated, with guardrails and audit evidence.
Remediation workflows that respect release cycles and operational constraints.
Integrate into Git, IaC and pipelines to prevent drift from shipping.
A living control plane where detection, policy and remediation come together.
Simulate remediation and validate posture improvements before rollout.
Get started
Shadow Phantom is built to become the system of record for security ownership. A living control plane where detection, policy and remediation come together.